The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic.
A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale.
At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks.
Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system.
In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit.
During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request.
This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power.
DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target.
In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet.
The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said:
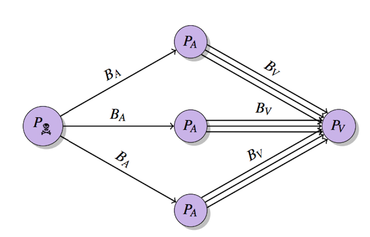
“An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim.
The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.”
In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team.
In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times.
Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/


